In today’s digital world, phishing attacks have become one of the most common—and dangerous—forms of cybercrime. These attacks trick users into revealing sensitive information such as passwords, banking details, or company data by pretending to be a trusted source.
Whether you’re an individual user or a growing business, understanding how phishing works is the first step toward preventing it.
A phishing attack is a fraudulent attempt to steal data by disguising as a legitimate email, message, website, or caller.
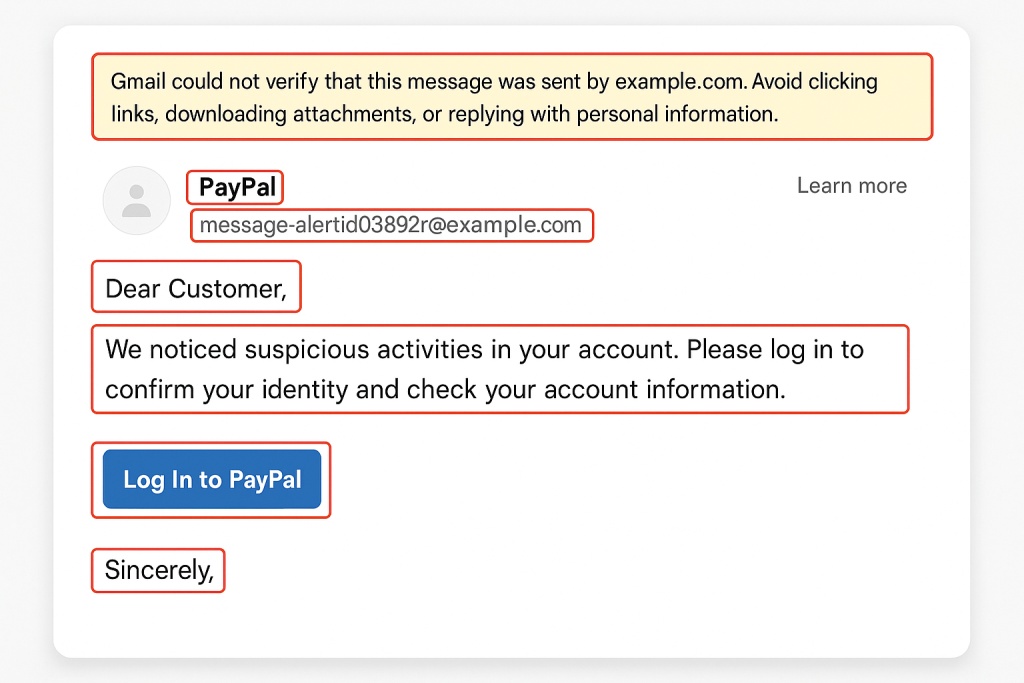
Cybercriminals often create fake emails designed to look real—complete with logos, sender names, and official language.
The goal?
To make you click, download, or share something you shouldn’t.
A mid-level employee received what looked like a routine invoice email from a known vendor.
The email was well-designed, carried the vendor’s name, and even had an invoice number.
Without verifying, the employee clicked the link and entered company credentials on a fake login page.
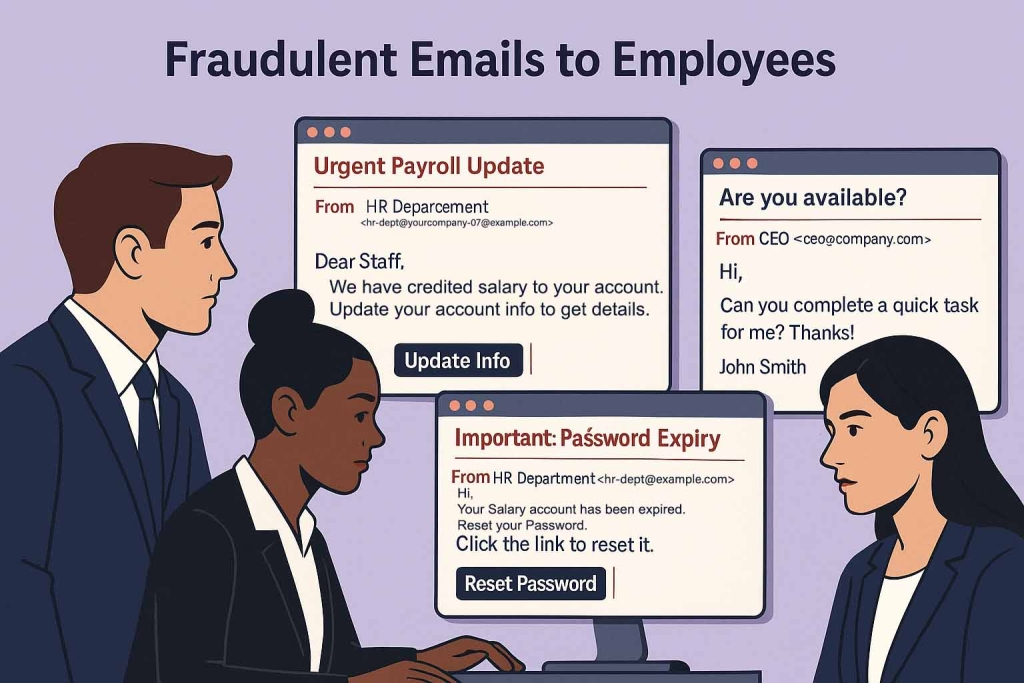
This is a classic example of how a single click can impact an entire organization.
Look out for these common warning signs:
If something “feels off,” it probably is.
Strong awareness and simple habits can protect individuals and organizations.
Always double-check the email address, not just the display name.
If unsure, contact the sender through another verified channel.
Hover over links to preview the actual URL.
If it looks suspicious, don’t click.
Even if attackers get your password, MFA blocks access.
It’s one of the strongest defenses against compromised credentials.
Updates fix security vulnerabilities that attackers often exploit.
Cyber awareness training is essential for businesses—especially those handling payments or confidential data.
Quick action can prevent further damage.
Phishing attacks rely on one thing: human error.
By staying vigilant, verifying details, and adopting basic cybersecurity practices like MFA (Multi-Factor Authentication), you can significantly reduce your risk.
You can report cybercrimes in India at www.cybercrime.gov.in, an initiative of the Government of India. You can also call the National Cybercrime Helpline Number 1930 for immediate assistance, especially if you have lost money.
This simple awareness can save both individuals and companies from financial, reputational, and operational losses.
This is just the beginning of our Cyber-Safety Series. Follow along to stay one step ahead of cybercriminals.